Overview: HTTP Traffic from users to web sites and API's need to have WAF protection. Both Azure and AWS have good services to protect your API's and applications. There is also the option to use a dedicated WAF Services. When protecting large organizations with hybrid cloud providers then options like Barracuda, Imperva/Encapusla, F5 and Cloudflare are good enterprise level options. Fundamentally, a WAF sits as an intermediary between the user and the resource they are requesting using HTTP. I like to set my highest priority rule to DENY all HTTP & HTTPS traffic, then i specifically open the rules that i want to flow thru, a lot people do it the other way around in smaller implementations.
WAF Options:
- Azure WAF simple in 1 region for a WAF especially with APIM and if you are an Azure customer simple got for an Azure Application Gateway with WAF enabled. DDoS is s separate service that can be integrated before Azure WAF or Azure Firewall. Cheaper per IP SKU option for specific IP adrs.
- Azure Front Door WAF is pretty amazing, Cloudflare is historically the leader with similar functionality. On Microsoft Azure the main two options for WAF are Front Door WAF (Best, most expensive) and Azure Application Gateway WAF.
- Competitor options: Barracuda WAF SaaS Service or Any software firewall KEMP, F5, Check Point, Fortinet/Fortigate, Cloudflare WAF, Akamai, AWS WAF, AWS Network Firewall, Cloud Armor is GCPs WAF I believe, ....
- Check WAF service has protection at least for DDoS, XSS, SQL injection attacks, SSL Termination if you need it, Managed RuleSets.
- AWS WAF is for web traffic (layer 7), there is a separate AWS Shield service that is used for DDos attacks. AFS can be applied at a Application Load Balancer, Amazons API Gateway, and Amazon CloudFront. With AWS WAF you also get Shield (standard free). Shield adds advanced features and the standard version that is always included by default with AWS WAF has monitoring and DDoS protection.
- Barracuda WAF is a SaaS Service that has worked fairly well for me. Has a fair amount of options and rules. Has add-ons like anti-virus scanning.
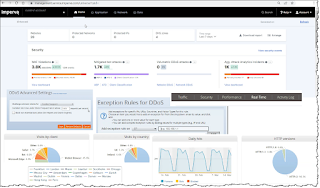
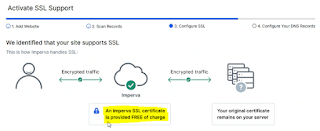
- Imperva WAF was previously called Incapsula WAF, that provides a SaaS WAF service including Smart DDoS (block dodgy traffic and passes thru good requests), API Security, SQL injections, Xss. Multiple data centers around the world.
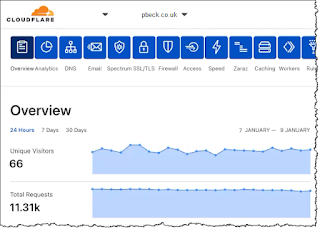
- Cloudflare is a Secure access service edge (SASE). Cloudflare provides a WAF service at hundreds of endpoints around the globe (for instance there are 5 Cloudflare endpoints in Australia). WAF functionality like SSL, DDoS (L7), customer rule e.g. rate limiting, OWASP rules applied, "api protection", et al. is done close to the user request (nice low latency) and then if successful it is pushed to the backend.
Last Updated: 2022-03-15



0 comments:
Post a Comment