Overview: Dynamics 365 CE (Customer Engagement) is a subset of the Power Platform and Dataverse. It provides commonly used entities such as Accounts and Contacts. There are five apps that can add specific CRM functionality. It is Microsoft's CRM solution.
There are 4 core subject (model) apps in Dynamics 365 CE
- Sales (MB-210) - client management including leads and turning:
- leads (Qualify step) into an
- opportunity (Develop step), goes to the
- Proposal step consists of generating quote, revising quote, marking acceptance, and invoice,
- Order created/lost (Closed step).
- Marketing (MB-220) - Lead generation & qualification, turn prospects in customers. Build campaigns to market your business. Email, social media, content creation to convert leads. Ensure you target the right audience using the correct channels and breaking leads into segments. I have only used this lightly and it is powerful. Events are useful for planning such as speakers and managing leads/event analytics. Referred to as Dynamics 365 Marketing. Customer Voice integrates with Marketing, e.g., embed survey sent our via email.
- Customer Service (MB-230)/Customer support - Dynamics 365 Customer Service - Low tough Customer Experience(Cx) and it also provides for high tough as needs demand, provides omnichannel options, chatbot, email, SMS, service requests, wiki's, phone in. Case management, raise record, route to where can be solved, and get to answer.
- Field Service (MB-240) - Dynamics 365 Field Service. Send people out to customer sites, schedule, ensure technician has work order and materials to complete the job.
Common Data Model - Agreed between various companies including Microsoft so there is a set schema that we use as a base for our businesses. Example entities:
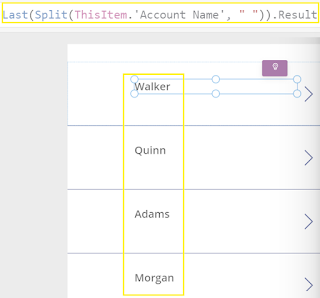
- Account - Company or individual (I think of this as a legal entity). Accounts have a primary contact, can have multiple contacts per account. Accounts can have parent accounts.
- Contact - is a person, can belong to multiple account.
LinkedIn Sales Navigator - Sync LinkedIn, so a contact changes, can be pulled into dynamics. Messages from Linked in are tract in dynamics.
Dynamics 365 Sales Insights - understand your relationships, and evaluate activities.
Dynamics 365 Customer Service / Customer Service Hub -
1) Raise a case via most suitable formats (align with SLA),
2) route case (align with SLA) e.g.,
3) Enter research such as calling customer, spoke to colleague against, knowledge base against the case. Lastly, can record fix e.g., called customer and walked them thru steps, and problem resolved
4) Close Case (includes reason)
Customer Service Notes
- Allows to integrate with other tools, ....
- Knowledge management - write articles in knowledge base (KB), submit for review, all staff can search to find fixes/info. Can also import from SharePoint, EpiServer, Wordpress and others into KB.
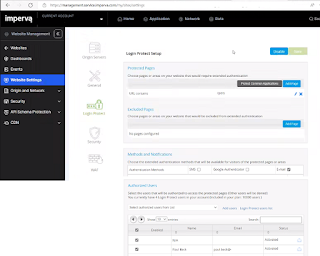
- Omnichannel - communication with customer on multiple channels e.g., Teams, SMS, virtual agent, social media. Hook into external channels also.
- Analytics - measure customer service activity. Show kpi's to show emerging topics, agent performance, how quickly cases are being resolved.
- Also has remote device management.
Dynamics 365 Field Service - Deliver on site service & manage workforce example is plumbing business or mining machinery maintenance. Importantly deals with scheduling & work orders. Deploy, fix issues/perform work from work order, the audit completion.
Note: MB-910 exam covers Dynamics 365 CE solutions. It is a simple exam that does not require annual renewal and gives the hold CRM Dynamics Fundamentals Status. The MB-210 specialises in the Dynamics 365 Sales and provides a Associate status which needs to be renewed annually with Microsoft.
There are specific solutions focusing on ERP (Think SAP (Enterprise), Oracle/JD Edwards (enterprise), Baan now Infor, Sage(small-medium), Dynamics 365 (small to medium), Workday (seems to be everywhere lately) ) focus on areas like Finance, Operations, Supply chain management, Machine maintenance. MB-920 covers the ERP fundamentals certification.